Model Context Protocol (MCP) is an open standard that allows AI models and applications to "plug into" external sources (like your files, databases, or software) to read data, modify records, and execute actions, all without needing custom-built code for each integration. From internal copilots querying company systems to external AI agents acting on users' behalf, MCP transforms APIs into interfaces ready for agents.
However, once you give these agents access with credentials, security becomes critical. An MCP endpoint protected only by static API keys or lightweight middleware checks like IP allowlisting is risky.
Developers require a straightforward way to secure an MCP service with proper token-based authorization, without becoming experts in identity infrastructure.
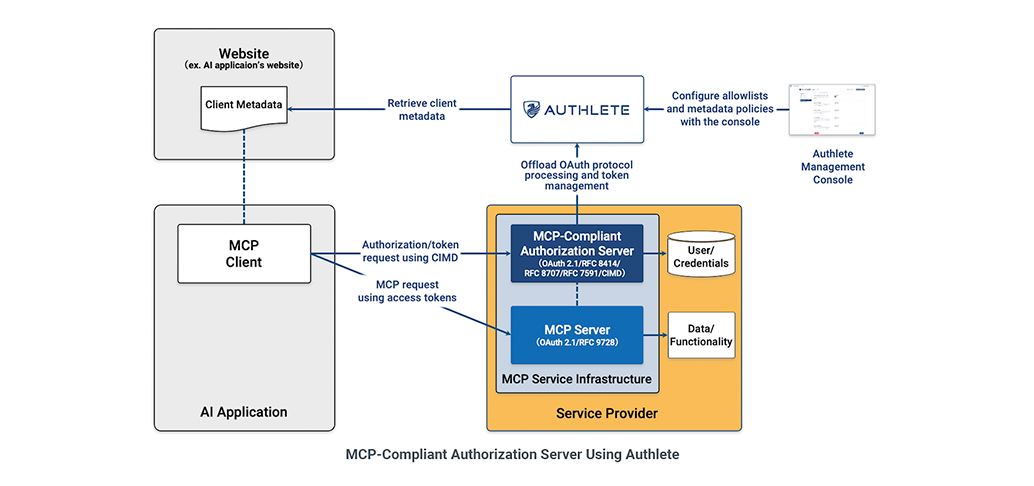
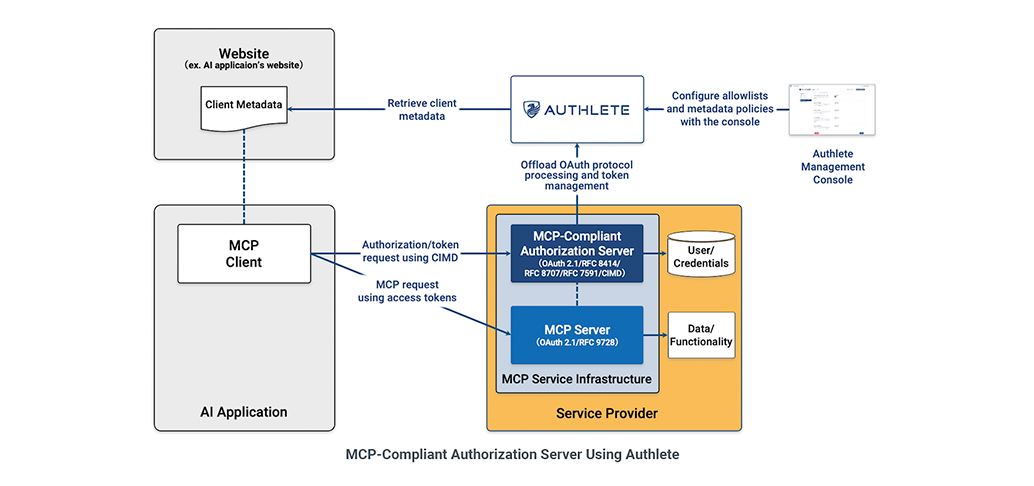
This article provides that path. We explain why MCP services require an OAuth authorization server, why that server should be compliant with Client ID Metadata Documents (CIMD), and how Authlete makes it easy to implement a secure MCP integration without building or maintaining a full OAuth stack yourself.
MCP, originally introduced by Anthropic, is an open protocol that enables AI agents to interact with external tools, data sources, and services in a structured, interoperable way.
Instead of hard-coding integrations, agents discover and invoke capabilities exposed by MCP services. Think querying databases, retrieving documents, triggering workflows, or performing software actions on behalf of users. In practice, an MCP service is simply a resource server that exposes capabilities.
The crucial detail is that those capabilities often involve sensitive operations, such as:
Once an agent can act in the world, the question shifts from "Can it call this API?" to "Should it be allowed to?" That is fundamentally an authorization problem.
Many early MCP deployments relied on shortcuts to solve this problem, such as static API keys, an implicit trust in clients, or application-specific access checks.
But these approaches break down quickly as systems scale or become multi-tenant. Without a dedicated authorization server, MCP services face two core risks: over-permissioned access with no way to express fine-grained controls, and unverified clients that the service can’t distinguish from malicious ones.
MCP itself does not address these risks. It lacks an expiration or revocation model for credentials, and has no audit trail of who authorized what. And AI agents, while using MCP, can chain actions, autonomously explore interfaces, and operate at machine speed. An agent granted excessive permissions may perform unintended operations long before any human notices.
OAuth 2.1 addresses these issues by introducing scoped, time-limited access tokens issued by a trusted authorization server.
Instead of trusting the client directly, the MCP service trusts the token.
Unfortunately, scoped tokens only solve part of the problem. When the client requesting those tokens is an AI agent that registers itself dynamically, you also need a way to govern how that client registers.
This is where a CIMD-compliant authorization server becomes essential.
Standard OAuth handles token issuance well, but was designed with a quieter assumption: Client registration is a controlled, human-administered process.
MCP breaks that assumption. In agent-driven ecosystems, clients can spin up dynamically, register themselves, and request broad permissions without any human in the loop. An OAuth 2.1 spec-compliant authorization server does not necessarily address this on its own. That's the gap CIMD is designed to close.
In MCP-style environments, CIMD redefines how client identity works. Instead of registering with the server, the client hosts a JSON metadata document at a URL, and that URL itself becomes the client ID. When a client initiates an OAuth flow, the authorization server fetches and validates the document from that URL on demand. No persistent registration database is required.
This moves control from server-side registration to client-hosted identity. And it gives authorization servers a foundation to apply their own validation policy on top of it.
Why does this matter for MCP? Consider a concrete scenario: an AI agent initiates an OAuth flow, presenting a client ID that points to a metadata document with overly permissive redirect URIs or unsafe metadata combinations. Without any validation policy in place, the authorization server fetches the document, accepts it, and issues tokens, even though the underlying configuration is insecure.
CIMD defines foundational security mechanisms (such as SSRF protection for metadata URLs and response size limits), but it does not prescribe how to evaluate client trustworthiness. In practice, you need a validation policy layer on top that can:
For a deeper look at the design rationale, see Authlete co-founder Takahiko Kawasaki's overview of CIMD metadata policy.
Without this kind of governance, unverified client identity poses a significant risk, especially in multi-tenant environments with unknown agents.
However, an authorization server with CIMD support and metadata policy enforcement solves the full lifecycle:
The above works well, and the lifecycle is clean on paper … but implementing it from scratch is prone to security errors.
Each layer carries its own implementation surface: PKCE (Proof Key for Code Exchange, a security extension that prevents authorization code interception), token signing and key rotation, metadata validation logic, and conformance testing. And as MCP specs evolve, so does the work of staying current.
Your authorization server needs all of this, but should you be the one building it?
Most teams developing MCP services want to focus on AI integration and business logic, not identity infrastructure.
Authlete is a specialized, API-first authorization engine. It provides the OAuth/OpenID Connect (OIDC) engine for your application, meaning you don't host or operate the protocol layer at all. Protocol correctness, token management, and CIMD-based metadata policy enforcement are handled out of the box. As MCP's authorization requirements evolve, Authlete absorbs that complexity so you don't have to.
Getting started with Authlete is straightforward.
Setup occurs through the Authlete Management Console, where you configure your service's authorization parameters, define the scopes that map to your MCP capabilities, and register the clients (whether AI agents, applications, or both) that will request access.
From there, your application server connects to Authlete's APIs to handle the authorization flow. Authlete also provides a full example OAuth server implementation to accelerate the integration.
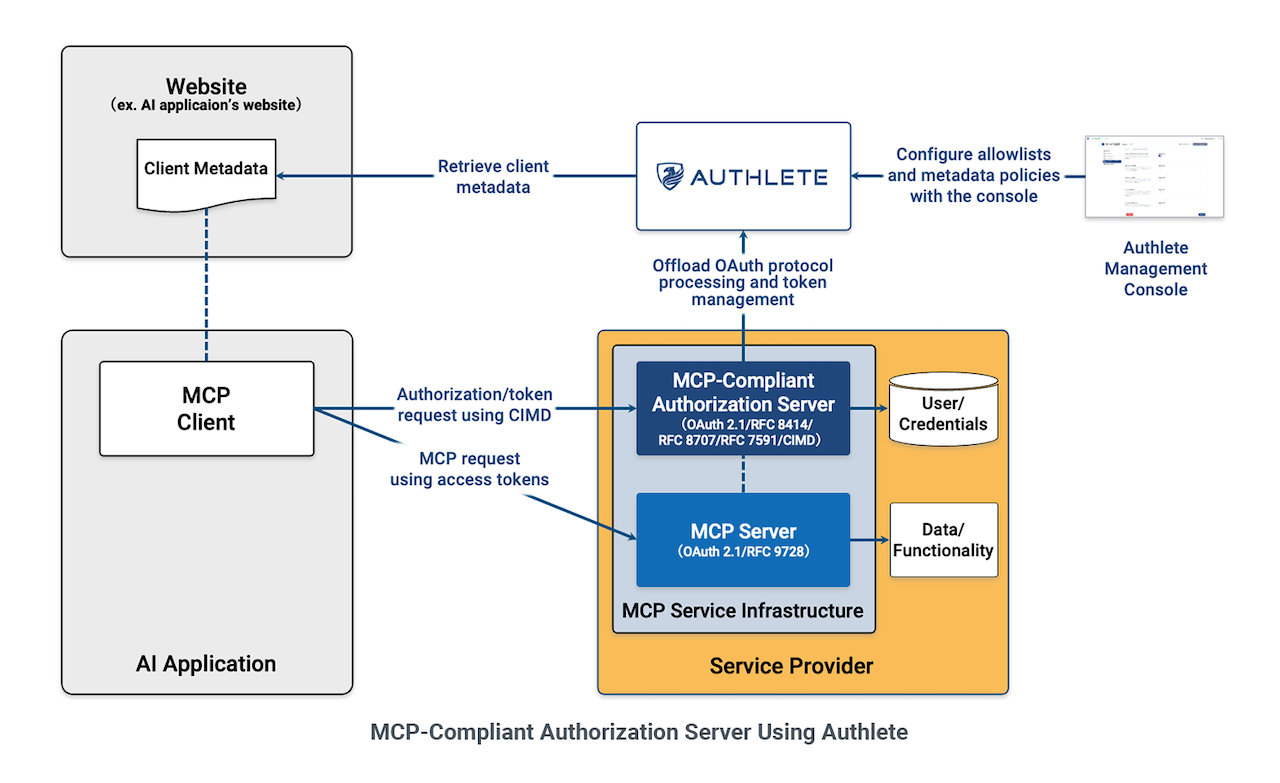
On the MCP service side, the integration footprint is small. The service validates bearer tokens by calling Authlete's token introspection endpoint. It never issues tokens itself, manages keys, or stores client data. Each request is allowed or denied based on whether the token is valid and has the required scope for the requested operation. That's the entire integration surface for the resource server.
Once Authlete is in place, the decision becomes how you carve up MCP permissions. This determines how precisely you can enforce least-privilege access for different clients and use cases. That's a product and architecture conversation, not an implementation one, and it's where engineering leadership tends to have the most useful input.
With all components in place, the end-to-end flow comes together cleanly. An agent registers as a client subject to CIMD policies, requests authorization on behalf of a user, and receives a scoped, time-limited token from Authlete. The MCP service validates that token and executes the operation only if scope and policy allow it. Your team's energy stays where it belongs: on MCP service logic and AI integration, not on OAuth infrastructure.
MCP ecosystems are moving fast, and the authorization layer is no longer something you can defer. The combination of OAuth 2.1 scoped tokens and CIMD-based client governance is emerging as the baseline for production-grade MCP deployments.
The good news is that the integration footprint is small and the path is straightforward: sign up for an Authlete account, configure a service in the Authlete Management Console, define your scopes against your MCP capabilities, and wire up token introspection on your resource server. Most teams can get a working authorization layer running in a day without touching OAuth internals.
As your MCP service scales to more clients, more agents, and more sensitive operations, the value of getting this right early compounds. The teams that will move fastest aren't the ones who built their own auth stack. They're the ones who instead let a purpose-built authorization service handle it.
Get started with Authlete today. Sign up for a free trial here.